.png)
How It Works
By standardising supplier data, mapping thousands of organisations onto a living network, and overlaying proactive threat intelligence, Risk Ledger’s four-stage approach is transforming fragmented TPRM into Active Supply Chain Security.
.png)
By standardising supplier data, mapping thousands of organisations onto a living network, and overlaying proactive threat intelligence, Risk Ledger’s four-stage approach is transforming fragmented TPRM into Active Supply Chain Security.
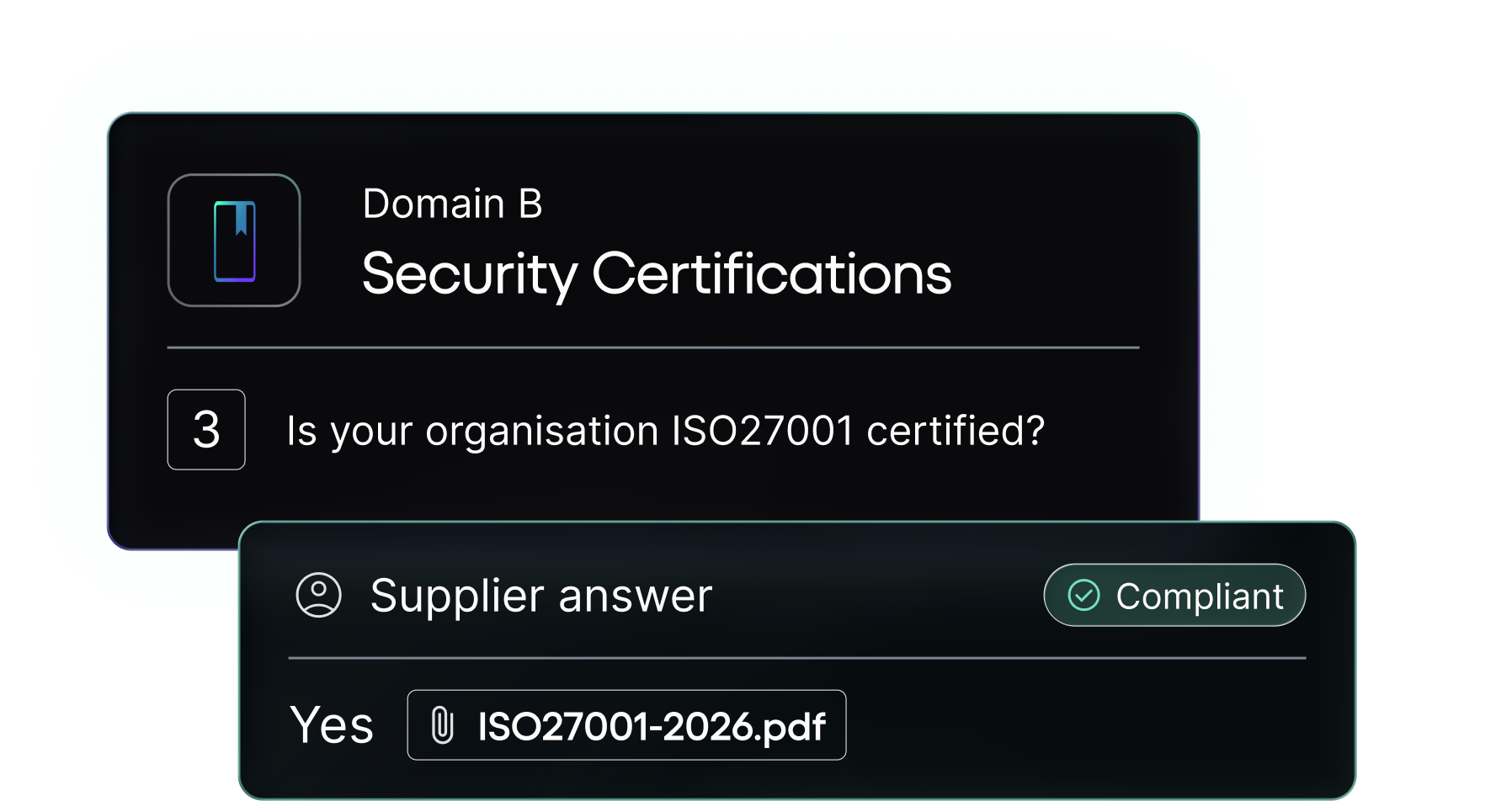
Standardise supplier assessments
Suppliers complete one security profile on the Risk Ledger platform, update it regularly, and share it across the network. These uniform assessments create a common language of risk, simplify due diligence and accelerate supplier onboarding.
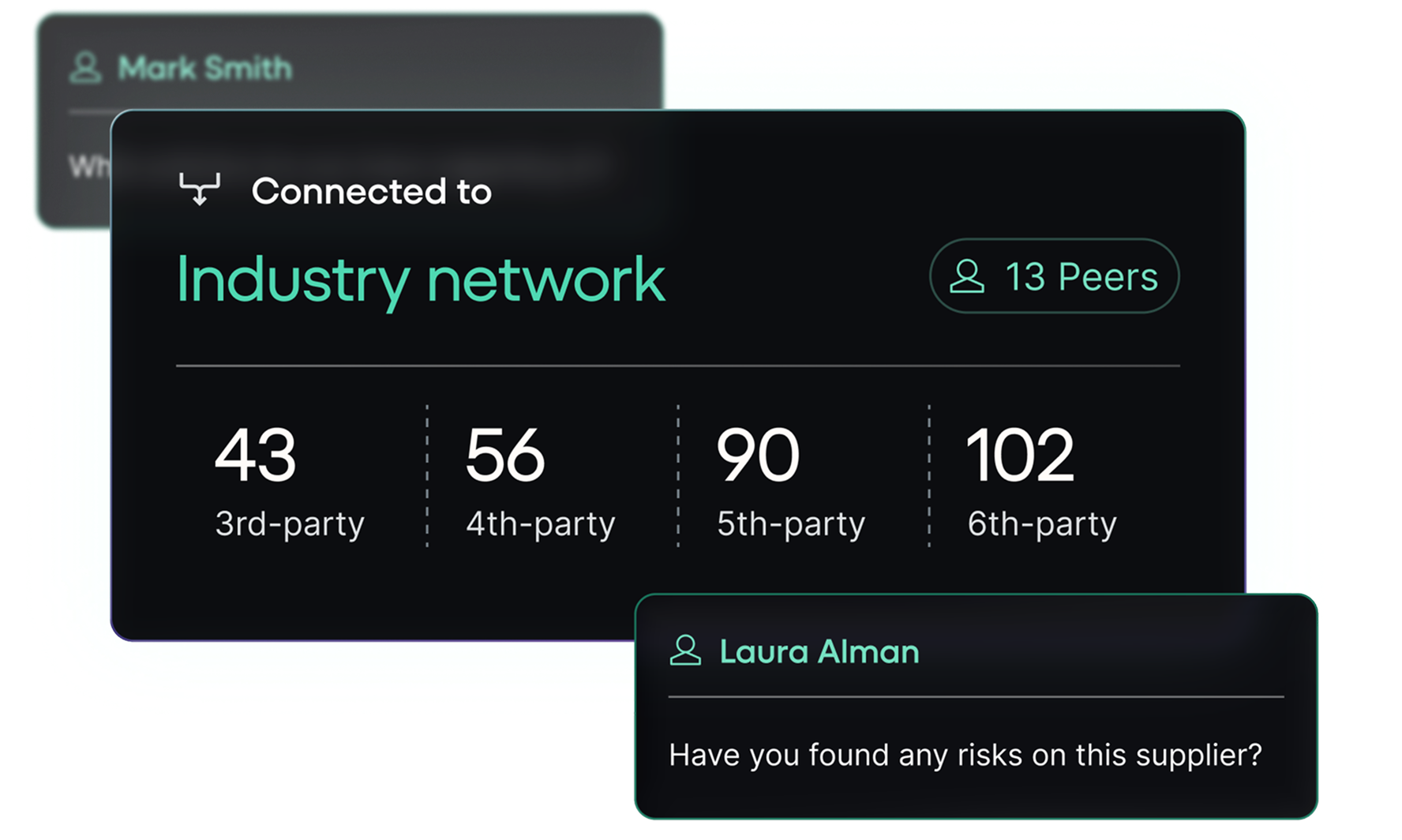
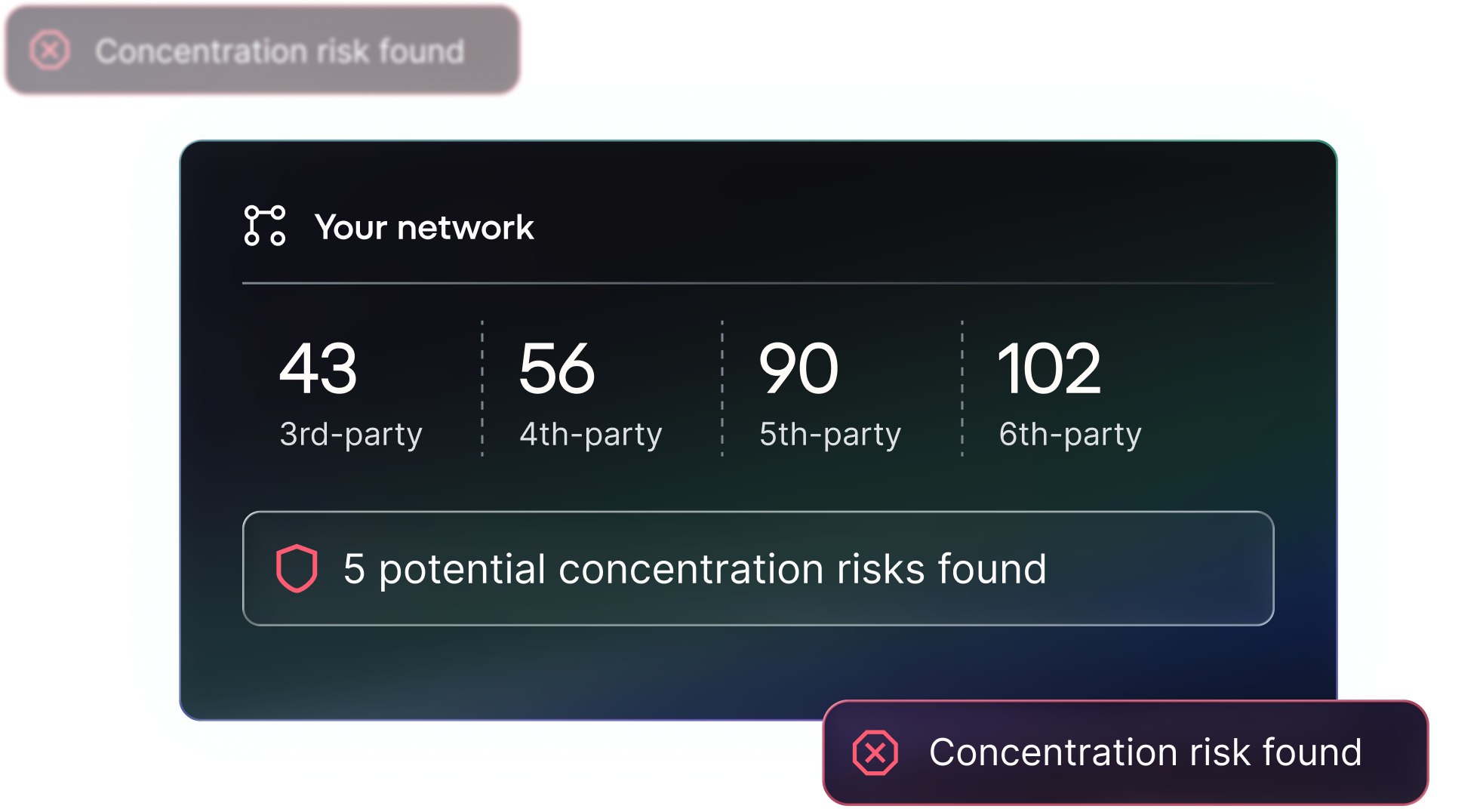
Visualise the supplier network
Risk Ledger’s platform maps thousands of organisations on a living interconnected database. This shows your supply chain as it truly exists, uncovering hidden nth-party relationships and concentration risks.
Detect supply chain threats in real-time
Risk Ledger overlays new vulnerabilities and attacks emerging threats onto the network map in real-time and sends platform alerts to impacted organisations. This reveals the cascading network exposure and enables you to prioritise remediation.
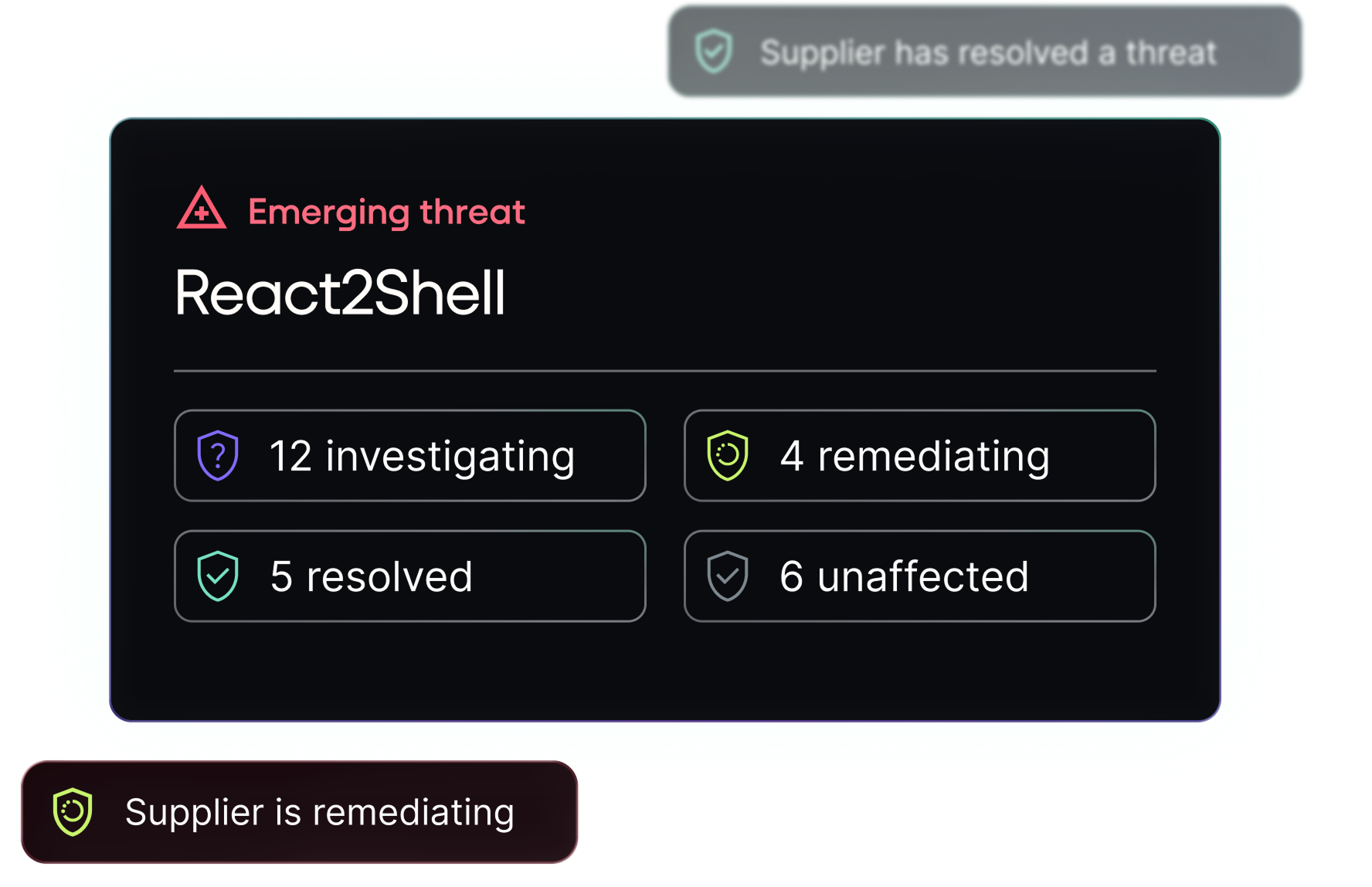
Defend-as-One
Risk Ledger’s platform enables collaboration and intelligence-sharing with the wider ecosystem. This collectively optimises resources, removes roadblocks to mitigation action and enhances security for every link in the chain.